The Rise of Self-Driving Technology
Autonomous driving technology is rapidly evolving, promising a future where vehicles navigate roads without human intervention. This transformative technology hinges on a complex interplay of sensors, sophisticated algorithms, and robust communication systems. The potential benefits are immense, including improved safety and efficiency on our roads. This innovation is not just about driverless cars, but also extends to various applications, such as delivery services and public transportation. The development of autonomous vehicles requires significant investment in research and development, as well as addressing the ethical and societal implications of this emerging technology.
Early adopters are already experiencing the advantages of autonomous driving features, such as adaptive cruise control and lane keeping assistance. These features represent stepping stones towards fully autonomous vehicles, offering valuable insights and lessons for the future. The process of developing and implementing autonomous driving systems is a complex and multifaceted undertaking, demanding a concerted effort from various stakeholders. From engineers and researchers to policymakers and consumers, everyone has a role to play in shaping the future of transportation.
Key Components of the Ecosystem
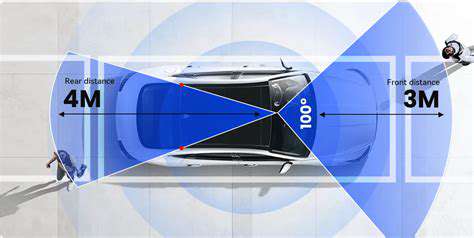
The autonomous driving ecosystem is a multifaceted network of components working together. These components include sophisticated sensors, such as lidar and radar, for perceiving the environment around the vehicle. These sensors provide critical data for the vehicle's navigation and decision-making systems. Advanced algorithms are essential for processing sensor data and enabling the vehicle to make informed decisions about its actions and trajectory. Robust communication systems are also crucial, connecting the vehicle to the infrastructure and other vehicles, enabling real-time information exchange and collaboration.
Another significant aspect is the development of robust infrastructure to support autonomous vehicles. This includes the creation of standardized communication protocols and the establishment of dedicated infrastructure for autonomous vehicles.
Furthermore, the safety and security of autonomous driving systems are paramount. Rigorous testing and validation procedures are essential to ensure the reliability and safety of these systems. Continuous monitoring and improvement are critical to adapting to the ever-changing environment and enhancing the reliability and performance of autonomous driving technology.
Challenges and Future Considerations
Despite the promising potential, numerous challenges remain in the development and deployment of autonomous driving technology. One significant hurdle is ensuring the safety and reliability of these systems in unpredictable and dynamic environments. Dealing with unexpected situations and maintaining safety in all conditions is a priority.
Addressing ethical dilemmas that may arise in complex situations is also crucial. For example, how should an autonomous vehicle respond in a situation where an accident is unavoidable? Establishing clear guidelines and protocols is essential to ensure that autonomous vehicles make responsible and ethical decisions in these challenging scenarios. The development of robust regulatory frameworks and standards is necessary to ensure safety and accountability.
Furthermore, ensuring widespread public acceptance and trust in autonomous driving technology is critical for its successful integration into society. Clear communication and education are essential to address public concerns and build confidence in this emerging technology.
The future of autonomous driving hinges on overcoming these challenges and fostering collaboration among stakeholders. Continued research and development, coupled with thoughtful policymaking, are essential to unlock the full potential of this transformative technology.
Data Integrity and Privacy Concerns in Edge Computing
Data Integrity in Edge Computing
Ensuring data integrity in edge computing environments is paramount, as data is often collected, processed, and stored at the edge of the network. This distributed nature introduces unique challenges compared to traditional centralized systems. Errors or malicious modifications at any point in the data pipeline can compromise the reliability of the entire system. Robust mechanisms for data validation, checksumming, and encryption are crucial to prevent data corruption and ensure the accuracy of information processed and transmitted throughout the edge network. This is critical for applications requiring precise and reliable data, such as industrial automation, healthcare monitoring, and autonomous vehicle navigation.
Implementing secure data storage and retrieval protocols at the edge is another key aspect of maintaining integrity. Edge devices often operate in isolated environments, requiring tailored security measures to protect sensitive data from unauthorized access or manipulation. Robust access controls, encryption keys, and secure communication channels are vital to prevent data breaches and ensure the trustworthiness of the processed information. This is especially relevant for applications dealing with sensitive personal or financial data.
Privacy Concerns in Edge Computing
Privacy concerns are significantly amplified in edge computing due to the decentralized nature of the architecture. Data collected at the edge is often sensitive and personal, raising concerns about data breaches and unauthorized access. Protecting user privacy requires careful consideration of data minimization, anonymization techniques, and secure data handling procedures at the edge devices themselves.
Compliance with privacy regulations like GDPR and CCPA is essential for organizations deploying edge computing solutions. Implementing appropriate data governance policies and ensuring transparency in data collection and usage practices are crucial to build trust and maintain compliance. Organizations must be mindful of the legal and ethical implications of collecting and processing data at the edge, particularly when dealing with personal or sensitive information.
Security of Edge Devices
Edge devices, often deployed in remote or resource-constrained environments, are vulnerable to various security threats. These devices, due to their limited computational resources and often less sophisticated security features, are attractive targets for attackers. Implementing robust security measures on these devices is essential to prevent unauthorized access and data breaches. This includes employing strong authentication mechanisms, regular security updates, and intrusion detection systems tailored to the specific functionalities and vulnerabilities of each edge device.
Data Transmission Security
Secure data transmission across the edge network is critical to maintaining data integrity and privacy. Data transmitted between edge devices, gateways, and the cloud often traverses insecure networks, making it vulnerable to interception and manipulation. Implementing encryption protocols, secure communication channels, and authentication mechanisms throughout the entire data transmission pipeline is essential to protect data from unauthorized access or modification. A robust end-to-end security approach for data transfer is vital for preventing data breaches and maintaining the confidentiality of the information being exchanged.
Data Storage and Management at the Edge
Secure storage and management of data at the edge are crucial for maintaining data integrity and privacy. Edge devices often store sensitive data locally, requiring robust security measures to protect against physical theft or unauthorized access. Implementing secure storage solutions, including encryption at rest and in transit, is vital for safeguarding data. Data loss prevention (DLP) strategies should be integrated to detect and prevent unauthorized data exfiltration. Implementing proper data retention policies and secure deletion mechanisms are also necessary for compliance with data privacy regulations.
Addressing the Challenges of Scalability and Interoperability
As edge computing deployments grow in scale and complexity, ensuring interoperability and maintainability across different devices and platforms becomes increasingly important. Developing secure, interoperable protocols and standards is crucial to enable seamless data exchange and processing across heterogeneous edge environments. Furthermore, scalability of security measures must be considered as the number of edge devices and data volume increases. Solutions must be adaptable and resilient to accommodate future growth and technological advancements in the edge computing landscape. This requires careful consideration of both technical and organizational aspects to maintain security and privacy in evolving edge deployments.
Addressing the Challenges of Hardware Vulnerabilities
Hardware Trojans: A Silent Threat
Hardware Trojans, insidious defects deliberately introduced into integrated circuits (ICs), pose a significant and often overlooked threat to the security of autonomous systems. These vulnerabilities can manifest in various forms, from simple logic alterations to sophisticated backdoors enabling unauthorized access and control. The insidious nature of these attacks lies in their covert nature; they can remain undetected for extended periods, silently compromising the integrity and reliability of the hardware, potentially leading to catastrophic failures or malicious actions within autonomous systems, like self-driving vehicles or critical infrastructure control systems.
The potential impact of hardware Trojans is profound. They can enable attackers to manipulate sensor readings, compromise decision-making processes, or even gain complete control of the system. This is particularly concerning in autonomous systems where the consequences of compromised hardware could range from minor inconveniences to life-threatening situations, highlighting the critical need for robust hardware security measures throughout the design and manufacturing process.
Manufacturing Defects and Supply Chain Risks
Beyond malicious intent, manufacturing defects within the hardware itself can also introduce vulnerabilities. These defects, often stemming from flawed manufacturing processes, can lead to unintended behaviors that compromise the security of an autonomous system. These imperfections, while unintentional, can be exploited by attackers, creating opportunities for unauthorized access or manipulation. The complexity of modern integrated circuits and the intricate manufacturing processes involved increase the likelihood of such defects and underscore the importance of rigorous quality control and testing procedures at every stage of the supply chain.
Furthermore, vulnerabilities can be introduced into the supply chain. If a component supplier unknowingly incorporates flawed or compromised hardware, the entire system's security is at risk. Secure supply chain management practices, including rigorous vetting of component suppliers and robust security audits, are essential to mitigate this risk. This includes ensuring that suppliers themselves adhere to stringent security standards to prevent the inadvertent introduction of vulnerabilities into the final product.
Countermeasures and Mitigation Strategies
Addressing the challenges of hardware vulnerabilities necessitates a multi-faceted approach encompassing design-level countermeasures, robust testing methodologies, and secure supply chain practices. Employing formal verification techniques during the design phase can help identify and mitigate potential vulnerabilities at the source. This involves rigorous simulations and analyses to ensure the intended functionality of the hardware aligns with the security requirements. Additionally, sophisticated testing protocols, including hardware fault injection and security testing, are crucial to uncover and validate the resilience of the hardware against various attack scenarios.
Implementing secure manufacturing processes and supply chain management is equally important. This involves employing secure component selection criteria, including thorough supplier vetting and security audits. The use of secure design methodologies and rigorous quality control processes can help to reduce the likelihood of defects and vulnerabilities being introduced into the hardware during manufacturing and throughout the supply chain. This multifaceted approach is essential to ensure the security and reliability of autonomous systems against hardware-based threats.